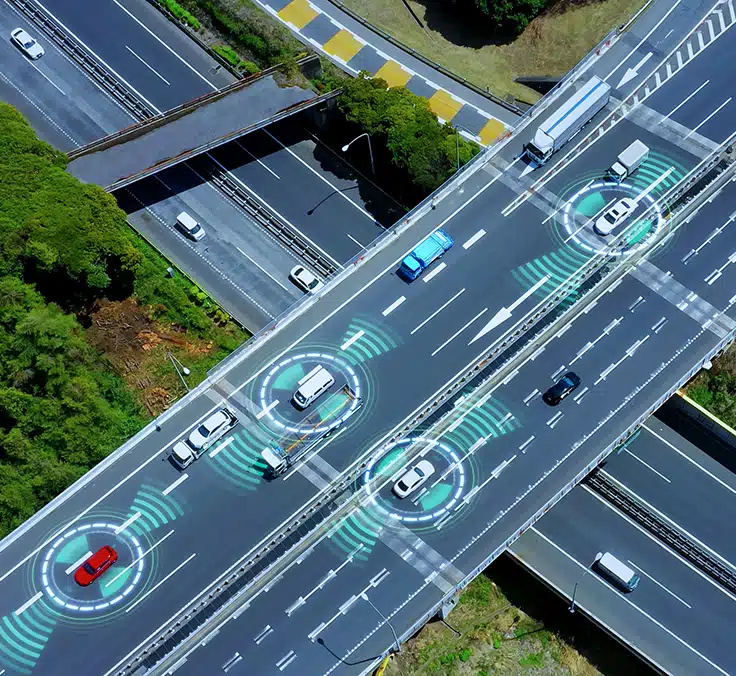
As vehicles become increasingly connected, we are witnessing a radical change in the way that users interact with their means of transport. This innovation, beyond improving the driving experience with advanced services, is helping to increase efficiency and safety on the road.
However, the progress toward total connectivity between vehicles is raising some cybersecurity concerns. Could our cars be hacked? What would the consequences be in terms of security? Connectivity makes vehicles more susceptible to a wide range of cyber threats, which poses a challenge for manufacturers as well as drivers and regulators, and even a potential problem for pedestrians in the event of hacking.
What exactly do we mean by connected cars? Connected cars are vehicles that communicate with each other and exchange information with their environment, essentially making them mobile data centers. They are basically computers on wheels, capable of receiving remote software updates that impact driving in one way or another (for example, in navigation, security systems, etc.).
The dark side of connectivity: risks and vulnerabilities
Despite the undeniable advantages, connectivity in these types of vehicles opens the door to possible cyberattacks. What can they consist of? The consequences of unwanted remote access could range from personal data theft to the occupants’ physical safety being compromised if the system is maliciously hacked. Incidents such as the hacking of a Jeep Cherokee in 2015 highlight the reality of these threats and the need to adopt protective measures.
One of the biggest threats in vehicle cyberattacks is remote access: hackers can access the system in several ways, such as exploiting vulnerabilities in the vehicle’s software, targeting car owners with phishing techniques, or directly intercepting communication between the car and network. What could happen if my car is hacked? There is a wide range of potential consequences. In the best-case scenario, cyberattackers could steal the driver’s personal data; in the worst case, they could seize control of the vehicle’s systems remotely, causing a potential accident, which is what happened with the aforementioned Jeep.
Regulatory framework for cybersecurity in cars
To address these new threats, international regulatory frameworks and regulations have been established to reinforce the cybersecurity of connected vehicles. Standards such as ISO/SAE 21434, Regulations 155 and 156 of the UNECE World Forum for Harmonization of Vehicle Regulations (WP29), and the SERMI (“Forum for Access to Security-Related Vehicle Repair and Maintenance Information”) procedure are decisive, providing risk management guidelines and requiring manufacturers to continuously update their security systems.
The ISO/SAE 21434 standard, the result of collaboration between the International Organization for Standardization (ISO) and the Society of Automotive Engineers (SAE), establishes a comprehensive framework for addressing cybersecurity throughout the life cycle of connected cars. This standard emphasizes risk identification and management, security measures, and an agile response to cybersecurity incidents. Through this comprehensive approach, cybersecurity is considered paramount in the development and maintenance of vehicles, that is, throughout their life cycle.
Complementing this initiative, Regulations R155 and R156 establish specific requirements for cybersecurity management systems and software updates. While R155 focuses on protecting vehicles against cyberattacks and managing incidents efficiently, R156 ensures that software updates are performed securely, without introducing additional vulnerabilities. Furthermore, the SERMI procedure – only mandatory in the European Union – provides a mechanism to ensure that repair and maintenance information can be accessed securely. This allows authorized repair shops (multi-brand and independent dealers) to perform repairs without compromising the vehicle’s integrity.
With the publication of ISO/SAE 21434 in August 2021, these services and providers are expected to start adopting their guidelines progressively. These regulations require them to assess risks, implement a cybersecurity management system, and develop procedures to respond to incidents and vulnerabilities. This comprehensive approach ensures that security is not limited to the design or production phase, but is maintained as a continuous process throughout the vehicle’s life span.
UNECE Regulations R155 and R156 introduce requirements for manufacturers to implement cybersecurity management systems and to manage software updates securely. To sell vehicles in the EU, manufacturers have had to comply with this regulation since January 2022 for new approvals, while the obligation will extend to all new cars from July 1, 2024. Meanwhile, the SERMI procedure has been applied in Spain since April 2024, when companies were accredited nationally to assess independent operators and guarantee secure access to repair and maintenance information.
Manufacturers' initiatives to guarantee security
Vehicle manufacturers are aware of this new reality and have developed cutting-edge security measures, such as intrusion detection systems, data encryption, and safeguards against the possible manipulation of a vehicle’s software. For example, vehicles equipped with facial detection systems allow keyless access by recognizing the face of the authorized driver or occupants. When a person approaches the vehicle, an exterior camera captures their image and compares it with a database of authorized faces stored in the vehicle’s system. If there is a match, the doors are automatically unlocked.
These new initiatives include the adoption of intrusion detection systems and data encryption protocols and the development of secure management systems for software updates. Intrusion detection systems constantly monitor the vehicle’s network in search of suspicious activities, allowing a quick response to possible attacks. Data encryption protects the vehicle’s personal and operating information, while the secure management of software updates ensures that improvements and corrections are implemented without introducing new vulnerabilities.
Furthermore, manufacturers are collaborating with technology partners and participating in platforms and consortiums for the exchange of information on cyber threats, such as the Automotive Information Sharing and Analysis Center (Auto-ISAC). These collaborations allow them to share and receive information on the latest threats and vulnerabilities, providing a joint response to cyberattacks.
What can car owners do to defend themselves?
Connected car owners can play a fundamental role in the cybersecurity of their vehicles with simple measures, such as keeping their vehicle's software updated, using Wi-Fi and Bluetooth connections with caution, not storing unnecessary personal information in the vehicle's system, and being on guard about phishing.
If you suspect that your vehicle has been compromised, it's important to immediately contact the manufacturer or dealer to report any anomalous behavior and seek advice. It may be advisable to temporarily disable the vehicle’s connected features, change your passwords for the associated accounts, and review these accounts for unusual activity.
CESVIMAP: Pioneers in automobile cybersecurity research
Mapfre’s R&D Center, CESVIMAP, offers resources and conclusions on research into cybersecurity in cars. Its focus on identifying vulnerabilities and formulating defense strategies is helping to make vehicles more secure, and this also extends to cybersecurity in connected cars.
“Connected cars with electrically controlled steering, brakes and engines, as well as electric chargers, are relatively easy to hack. The automotive sector is working to limit and control vulnerabilities, and at CESVIMAP we are supporting and advising them along the way,” said Enrique Zapico Alonso, Mapfre Mobility Lab Manager at CESVIMAP.
In short, cybersecurity in connected cars continues to evolve as threats increase. Synergies between the different players in terms of defense strategies are essential. By tackling these challenges together, they can ensure that progress toward smart and connected mobility is safe for everyone.